If you design, build or supply Military Command and Control C2, create a profile to showcase your capabilities and connect with visitors who have an active requirement for your solutions.
Suppliers: Military Command and Control C2

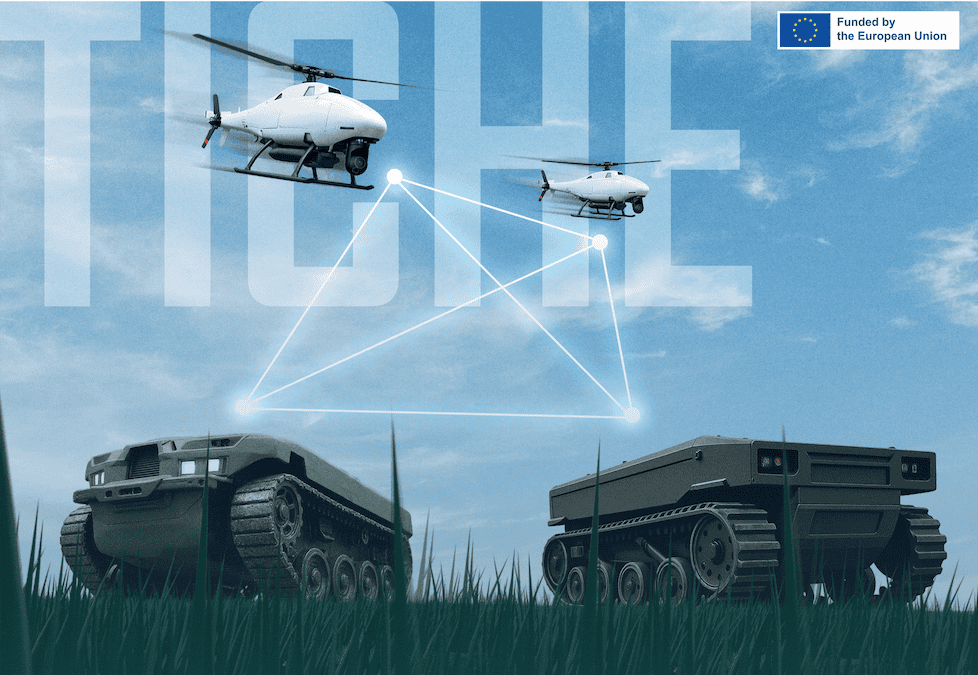
Innovative AI-powered Autonomy Solutions for Military Vehicles

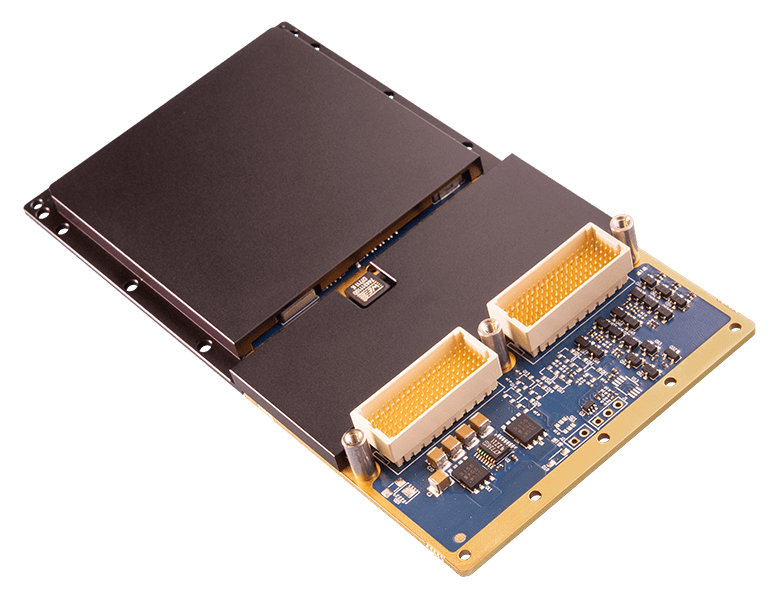
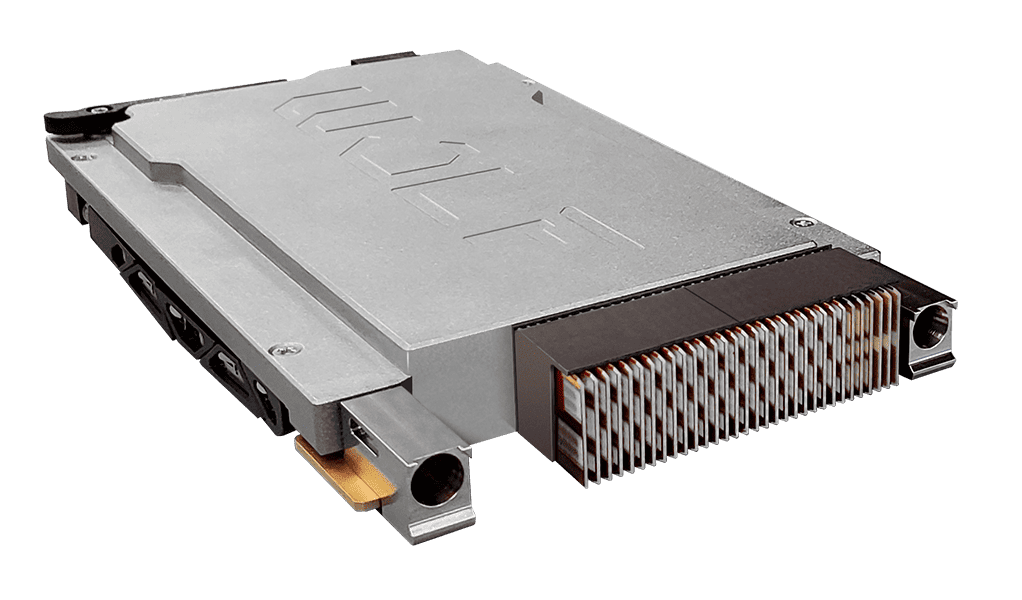
Ultra-Reliable & Mission-Proven Rugged Computing Solutions for Demanding Defense & Security Applications

Rugged High-Performance Computing & Video I/O Modules: 6U and 3U VPX, XMC, and VNX+ for Defense Applications

Advanced Solutions for Defense Modernization: Propulsion, Sensors, Communication & Augmented Reality Systems
Autonomous Military Robotics and Technologies | Amphibious Tracked Vehicles
Assured Position, Navigation and Timing (PNT) Solutions for Military and Defense

SIGINT Payloads & Software-Defined RF Sensing Technology for Military UxS

Reliable, Resilient and Secure Satellite Communications & Assured PNT Solutions for Mission-Critical Applications

State-Of-The-Art Flight Control & GNSS-Denied Navigation Technologies for Tactical UAV Platforms

Mission-Critical Hardware & Software Technologies for Enhanced Command & Control in Challenging Battlefield Environments

Pioneering Ground Control Stations (GCS), Electronics and Payload Solutions for Unmanned Systems and Defense Robotics
State-Of-The-Art Hyperspectral Imaging Cameras for Mission-Critical Applications

Next-Generation Marine Radar Processing Solutions for Enhanced Situational Awareness in Naval & Defense Applications

Rugged Hardware & HMI Equipment for Mission-Critical Military, Naval & Defense Applications
Thermal Imaging Solutions Featuring Cutting-Edge Intelligent Sensing & Threat Detection Technologies

Ultra-Reliable & Secure BVLOS Communications Technology for Mission-Critical Drones & Robotics

WE ARMOR IT. MilSpec Electronics & Rugged IT Equipment for Military, Government & Critical Infrastructure

Undersea Sensing, Communications, Imaging, Control and Navigation Solutions for Naval Forces

BLOS Strategic Communications Systems and Tactical Radio Range Extension Technologies
Powerful Edge Video Processing and AI-Powered Defense Solutions
Identification Friend or Foe & Mode 5 Combat ID for Military UAS

Mission-Ready, Blue UAS-Cleared & NDAA-Compliant Platforms for Defense, Government, and Security Operations

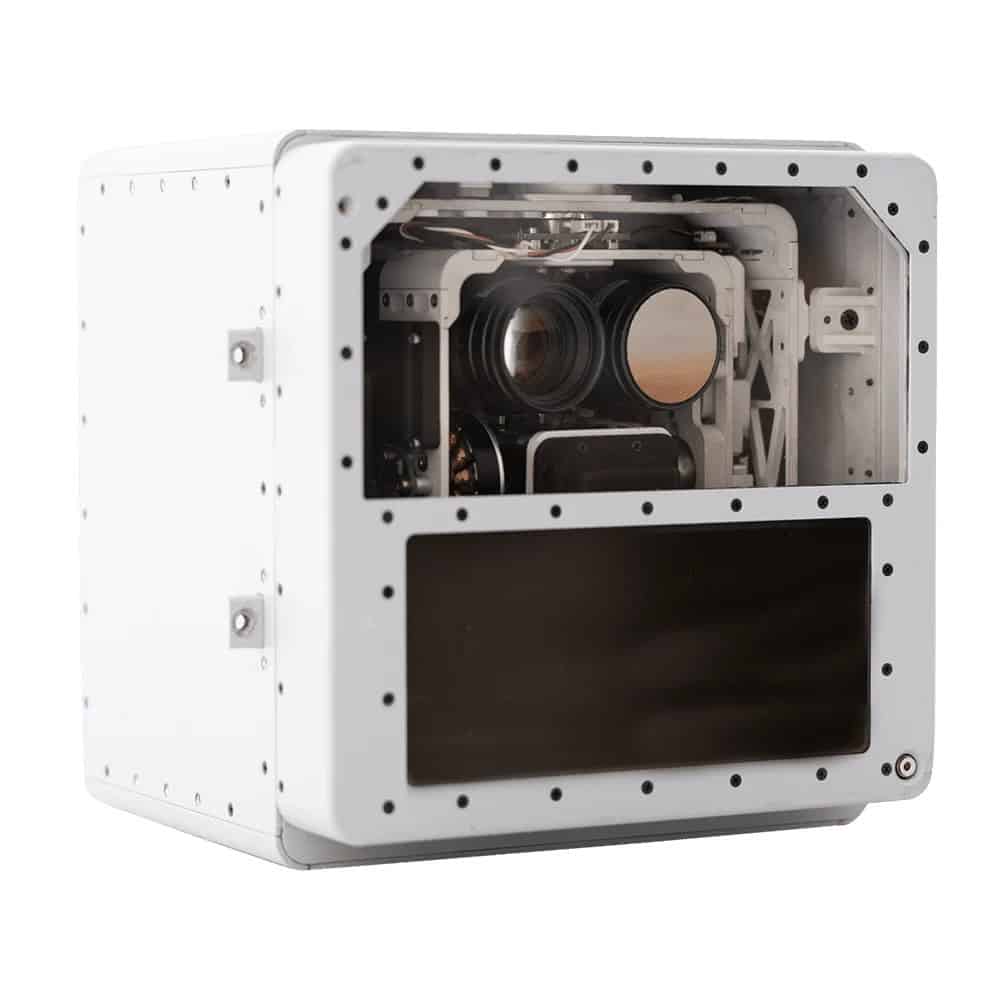
Advanced Imaging & Sensor Autonomy for Time-Critical Airborne Intelligence Missions

Rugged Computing Solutions for Mission-Critical Defense, Homeland Security, Law Enforcement & Emergency Response Applications

Mission-Critical Antenna, Tracking, & Video Solutions for Defense, Law Enforcement & Security Applications

Cutting-Edge Unmanned Aircraft Systems for Tactical Applications

State-Of-The-Art NDAA-Compliant Electronic Hardware Components for Mission-Critical Drone & Robotics Platforms. Made in the USA.

Bespoke Drone & Robotics Software Solutions for the Defense & Security Industries

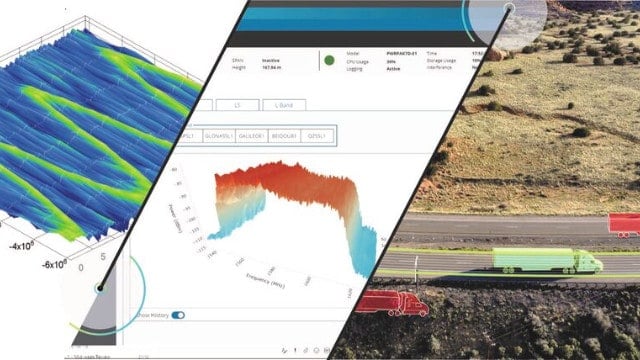
Geospatial Software Solutions for Mission-Critical Military, Defense & Security Operations

Mission-Critical Surveillance Data Solutions for Government, Military & Defense Organizations

Drone Parachutes & UAV Launch & Recovery Systems for Military & Defense Operations

NDAA-Compliant Software-Defined Ecosystem For Next-Generation Robotics & Autonomous Vehicle Platforms

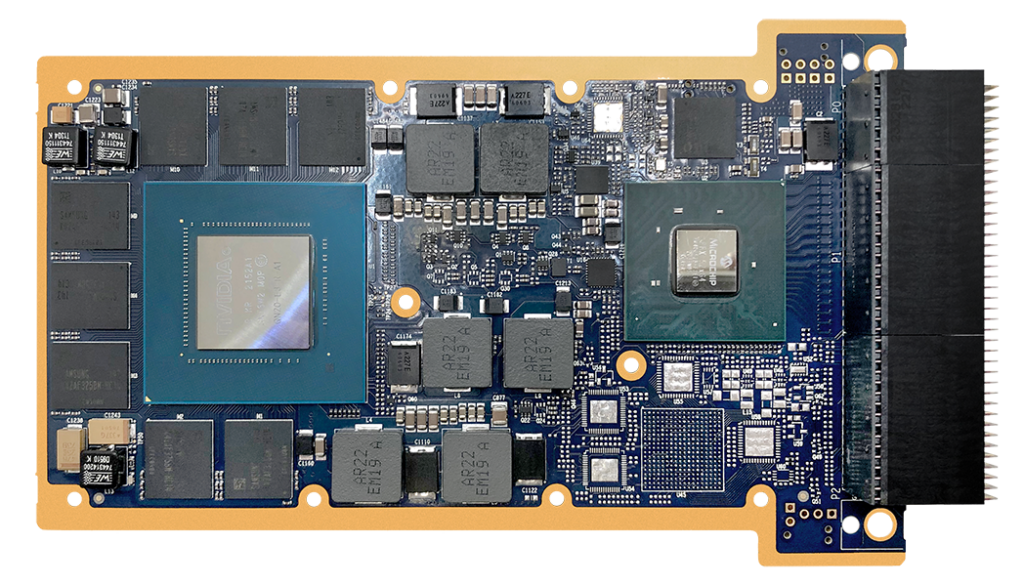
High-Performance Video Graphics, GPGPU, AI/ML Processing & Display Solutions for Mission Critical Environments

Advanced Mission Planner & Enhanced Ground Control Station for Modern Defense Environments

Global Provider of Certifiable Situational Awareness & BVLOS Solutions
Products
Military Command and Control (C2)
In this guide
Command and Control (C2) is defined by the US Department of Defense (DOD) as “the exercise of authority and direction by a properly designated commander over assigned and attached forces in the accomplishment of the mission”. C2 occurs at all levels of war from tactical, through to operational and strategic across all sea, land, air and space domains. Strategic-level C2 is exercised by a head-of-state/government or whichever individual is tasked as commander-in-chief. At the operational and tactical levels C2 will be exercised by military personnel.
Today’s military command and control blends human attributes and technologies, including specialized command and control software for mission planning, coordination, and real-time decision-making. The DOD definition continues that “(C2) functions are performed through an arrangement of personnel, equipment, communications, facilities and procedures employed by a commander in planning, directing, coordinating and controlling forces and operations in the accomplishment of the mission”. Personnel can include a commander and their staff at the headquarters, or equally a lieutenant and their sergeant at the tactical edge.
C2 Equipment & Technology
Battle Management Systems
C2 equipment typically includes Battle Management Systems (BMSs). A BMS is software depicting the placement of friendly, hostile, neutral and unidentified units cartographically. It provides details of the resources friendly units have at their disposal. The BMS can display reconnaissance information like imagery intelligence along with written situation reports from subordinate units. In short, a BMS provides a clearing house where all information pertinent to a mission or operation can be processed and disseminated. As highlighted below, communications are a key part of military command and control. They enable information and orders to flow around the battlefield. Procedures encompass everything from the prevailing doctrine governing how a particular force fights to written or spoken orders.
The OODA Loop
Observe, Orient, Decide and Act
Command and control depends upon the flow of information. A commander is given a mission. The mission is turned into the commander’s intent. Intent becomes a series of actions which will hopefully allow the mission to be accomplished. This series of actions are translated into orders. Orders are then transmitted to military units for their execution. Units execute the orders, the outcome of which is transmitted back up the chain of command. Commanders receive reports on the extent to which the orders have been successfully executed. They then adjust future orders based on these reports until the mission is accomplished.
In the 1950s the military theorist John Boyd distilled this cycle into the Observe, Orient, Decide and Act Loop. Better known as the OODA Loop this enabled C2 to emerge as a valuable force multiplier. Boyd posited that whoever navigates the OODA Loop the quickest in a military engagement is likely to prevail.
Boyd’s theory led to a steady expansion in the scope and sophistication of C2 technology helped by advances in digital technology from the 1960s onwards. This revolutionized the sophistication of the software, hardware and communications supporting C2.
C5ISTAR
Command, Control, Communications, Computers, Cyber & Intelligence, Surveillance, Target Acquisition and Reconnaissance
The industrial sector has since triggered a proliferation of acronyms to describe command and control. C2 became C3 with the addition of ‘Communications’. ‘Intelligence’ was merged with C3 creating C3I. The addition of ‘Computers’, ‘Intelligence’, ‘Surveillance’, ‘Target Acquisition’ and ‘Reconnaissance’ resulted in C4ISTAR. Most recently, ‘Cyber’ was added to create C5ISTAR.
These long acronyms are arguably pointless. The exercise of military command and control has always been dependent on intelligence, surveillance, target acquisition and reconnaissance. Likewise, communications are implicit in C2. Command and control cannot be exercised without transmitting orders whether via a state-of-the-art communications network or someone shouting orders above the noise of battle. Computers, and hence Cyber, are now such integral parts of C2 that, like communications, they hardly merit a mention. Relevant technology will change and augment over time, but the core C2 tasks will likely remain the same.
Command & Control Acronyms
C2 – Command & Control
- C2I – Command, Control and Intelligence
- C2ISR – Command, Control & Intelligence, Surveillance, Reconnaissance
- C2ISTAR – Command, Control & Intelligence, Surveillance, Target Acquisition and Reconnaissance
C3 – Command, Control & Communications
- C3I – Command, Control, Communications & Intelligence
- C3ISR – Command, Control, Communications & Intelligence, Surveillance, Reconnaissance
- C3ISTAR – Command, Control, Communications & Intelligence, Surveillance, Target Acquisition and Reconnaissance
C4 – Command, Control, Communications & Computers
- C4I – Command, Control, Communications, Computers & Intelligence
- C4ISR – Command, Control, Communications, Computers & Intelligence, Surveillance, Reconnaissance
- C4ISTAR – Command, Control, Communications, Computers & Intelligence, Surveillance, Target Acquisition and Reconnaissance
C5 – Command, Control, Communications, Computers & Cyber
- C5I – Command, Control, Communications, Computers, Cyber & Intelligence
- C5ISR – Command, Control, Communications, Computers, Cyber & Intelligence, Surveillance, Reconnaissance
- C5ISTAR – Command, Control, Communications, Computers, Cyber & Intelligence, Surveillance, Target Acquisition and Reconnaissance