If you design, build or supply Counter-IED Systems, create a profile to showcase your capabilities and connect with visitors who have an active requirement for your solutions.
Suppliers: Counter-IED Systems
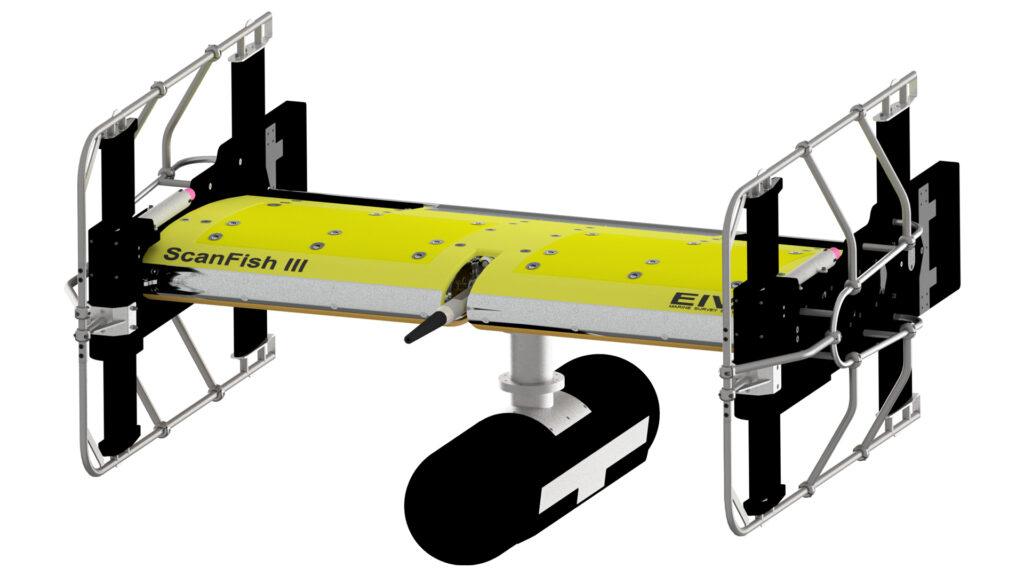
Undersea Sensing, Communications, Imaging, Control and Navigation Solutions for Naval Forces
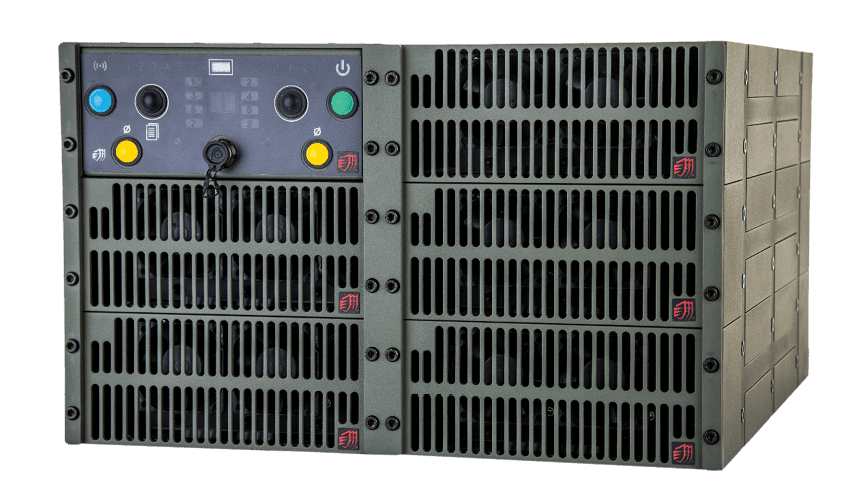
Electronic Countermeasures (ECM) & RF Jamming Technology for Protection from RCIED and Drone Threats
Products
Counter-IED Systems
In this guide
Introduction to Counter-IED Systems
Counter-IED (C-IED) systems are specialized technologies designed to detect, disrupt, and neutralize threats before they can compromise mission integrity. Combining electronic warfare, robotics, and advanced materials science, modern C-IED capabilities encompass the full operational cycle, including intelligence, detection, disruption, and post-blast analysis. By integrating distributed sensor networks and cognitive Electronic Countermeasures (ECM), these systems provide the force protection and mobility assurance necessary for operations in contested environments.
Core Counter-IED Capabilities
Detection and Identification Systems
Effective C-IED operations begin with the ability to identify concealed threats at a standoff distance. Modern detection suites utilize a layered sensor approach to maximize the probability of detection while minimizing false alarm rates.
- Ground-Penetrating Radar (GPR): This remains the primary tool for identifying buried metallic and non-metallic objects. Modern GPR systems analyze subsurface reflections to detect anomalies in soil density or the presence of pressure plates and casing materials.
- Electromagnetic Induction (EMI) and Trace Detection: Beyond simple metal detection, industry-standard Ion Mobility Spectrometry (IMS) and mass spectrometry are used to identify explosive residues at the molecular level.
- EO/IR and Hyperspectral Imaging: Optical and thermal sensors enable long-range visual detection of disturbed ground or thermal signatures from electronic components. When integrated into UAV or UGV payloads, these sensors extend the detection envelope well beyond the visual line of sight of the operator.
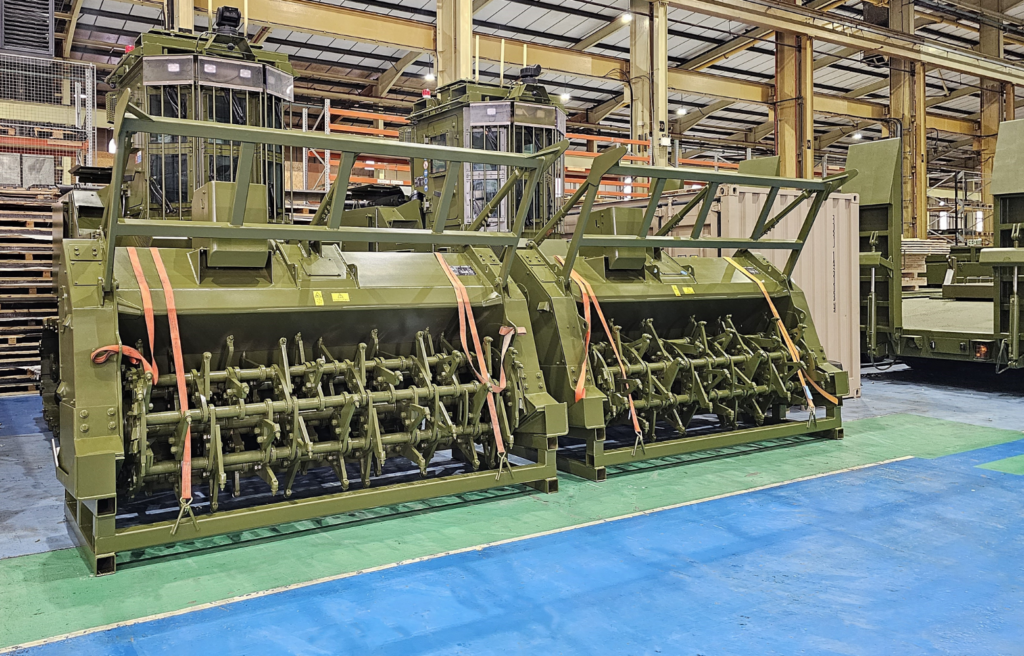
Neutralization and Disposal Technologies
Once a threat is identified, neutralization must be achieved with minimal risk to personnel. The focus has shifted heavily toward remote intervention.
-
Tactical EOD Robotics: Modern Explosive Ordnance Disposal (EOD) robots provide high-definition visual feedback and dexterous manipulation. These platforms are used for precision disruption, such as using water-jet disruptors to sever triggering circuits without detonating the main charge.
- Non-Kinetic Disruption: For Command-Wire IEDs (CWIEDs), which are traditionally immune to RF jamming, advanced C-IED equipment now utilizes galvanic detection and high-voltage discharge systems to neutralize physical firing leads.
- Blast Containment: In scenarios where in-situ neutralization is not possible, blast-resistant containment vessels and specialized EOD suits provide essential protection for technical specialists.
Anti-IED Vehicles
The platform carrying the C-IED equipment is just as vital as the sensors themselves. Vehicle design has shifted toward integrated survivability suites. Anti-IED vehicles, such as the MRAP (Mine-Resistant Ambush Protected) class, are engineered with V-shaped hulls to deflect blast energy away from the crew compartment. However, modern survivability now includes:
- Active Protection Systems (APS): To counter the threat of large-scale vehicle-borne IEDs (VBIEDs) and high-velocity projectiles, active systems can intercept threats before they reach the hull.
- Integrated Route Clearance: Dedicated IED detection vehicles combine GPR, mast-mounted EO/IR sensors, and robotic manipulator arms into a single, unified platform for route clearance operations.
Intelligent RCIED Jamming Solutions
Radio-Controlled IEDs (RCIEDs) represent a significant portion of the asymmetric threat. Counter-IED jammers must now operate in a dense electromagnetic environment, targeting everything from low-end VHF/UHF radios to sophisticated GSM, LTE, and satellite links.
Modern IED jamming has evolved from simple “barrage” jamming to intelligent RCIED jamming solutions. These systems utilize software-defined architectures to identify and prioritize threats in real time.
Smart Jamming and Cognitive ECM
Rather than flooding the entire spectrum, cognitive systems use threat libraries to recognize specific communication protocols. This “active” approach is more energy-efficient and allows for more effective suppression of emerging waveforms.
Signal Deconfliction and “Look-Through” Capability
A critical challenge in C-IED military operations is maintaining friendly communications while jamming the enemy. Advanced bomb jammers utilize “look-through” technology (precise, microsecond timing gaps in the jamming signal) to allow friendly signals to pass through without compromising the protective envelope.
Platform Integration
IED jammer vehicles provide 360° protection for convoys, while man-portable backpack systems protect dismounted patrols and EOD teams. These systems are increasingly designed around the Modular Open Systems Approach (MOSA) to ensure hardware can be updated as new threats emerge.
Future Trends in IEDD Technology
The future of Improvised Explosive Device Disposal (IEDD) is defined by the integration of AI and the reduction of Size, Weight, and Power (SWaP) requirements.
- AI-Enhanced Threat Prediction: Machine learning algorithms are being trained to recognize the subtle markers of IED placement in satellite and drone imagery, allowing for preemptive action.
- Networked C-IED Ecosystems: Future operations will see man-portable, vehicle-mounted, and aerial sensors sharing data in real time. This creates a “transparent” battlefield where a detection by a single drone can automatically update the jamming profiles of an entire convoy.
- Autonomous Swarms: UAV swarms are being developed to provide persistent overhead surveillance and rapid response for IED detection along critical supply routes.