If you design, build or supply Cyber Defense, create a profile to showcase your capabilities and connect with visitors who have an active requirement for your solutions.
Suppliers: Cyber Defense

Cutting-Edge Encryption Solutions for Military & Government: Protection Against The Most Sophisticated Modern Cyber Threats
Products
Military Cyber Defense
In this guide
Cyber defense is not just an essential component of modern military operations—it is a prerequisite for success in the digital age.
As militaries become increasingly reliant on digitized systems and interconnected networks, robust cyber defense technologies are required to address evolving threats. From protecting military networks and critical infrastructure to securing the Internet of Military Things (IOMT) and combat clouds, these solutions provide the resilience needed to maintain operational superiority. By embedding cybersecurity into the design and deployment of all digitized systems, militaries can safeguard their missions against the dynamic challenges of the cyber domain.
While digitization has revolutionized military operations, it has also introduced significant vulnerabilities. A hostile actor accessing military networks, software, or hardware poses severe risks. In peacetime, adversaries could steal, alter, or disrupt data to gain an intelligence advantage. During conflict, such attacks could render systems unusable, with catastrophic consequences at tactical, operational, or strategic levels. To mitigate these threats, robust cyber defense technologies are indispensable, ensuring military networks, data, and assets remain secure from adversarial manipulation.
Military Applications of Cyber Defense Technologies
Securing Military Networks
Digitized military systems, including the Internet of Military Things (IOMT), are highly interconnected, linking personnel, platforms, and sensors to shared combat clouds. This interconnection accelerates operational tempo by providing relevant data to users in real time. However, it also introduces potential vulnerabilities. Cyber defense technologies protect these networks through advanced encryption, intrusion detection systems, and secure communication protocols. For example, software-defined radios, which replaced earlier scrambling devices like the British Secraphone or German Enigma machines, now provide elaborate encryption for voice and data traffic.
Command and Control (C2) Systems Security
Cyber defense technologies secure computerized C2 systems like BMSs that transfer vast amounts of mission-critical data. These technologies ensure that operational orders, intelligence, and battlefield imagery are not intercepted, altered, or corrupted. Real-time monitoring and anomaly detection play key roles in safeguarding these systems from compromise during both peacetime and active operations.
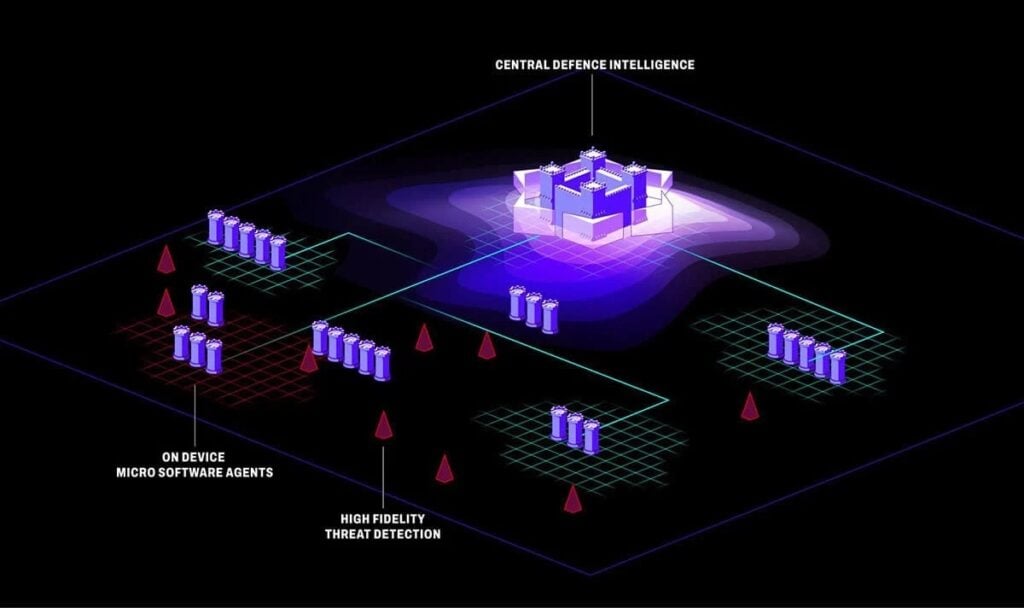
Countering Cyber Threats
Proactive cyber defense protocols aim to prevent attacks, minimize their impact, and identify perpetrators. Advanced tools, such as automated incident response systems and behavioral analytics, are pivotal in countering these threats. Threat intelligence platforms provide actionable insights, enabling military forces to adapt to evolving adversarial tactics.
Cyber-Physical System Resilience
As the military integrates digitized systems into weapons platforms, vehicles, and autonomous systems, cyber defense technologies ensure these assets remain operational under contested conditions. This is especially important in high-stakes scenarios where compromised systems could lead to mission failure. Autonomous systems such as UAVs and robotic ground vehicles rely on secure command and control links to prevent adversarial hijacking or interference.
Data Protection and Encryption
Data flowing through the combat cloud and IOMT requires robust encryption to prevent unauthorized access. Multi-layered cybersecurity measures, including advanced cryptographic protocols, secure data transfers while protecting against breaches. This is critical for maintaining operational secrecy and safeguarding sensitive intelligence.
Cyber Protection Strategies in Defense
Since the advent of widespread radio communication during World War II, securing military information has been a priority. Today, the focus has shifted to protecting digital traffic and computer systems against unauthorized access or manipulation. Cyber defense strategies encompass encryption, access control, and continuous monitoring to secure military communication and operations. For instance, early encryption devices like Enigma machines have given way to sophisticated cybersecurity architectures integrated into modern systems from the outset.
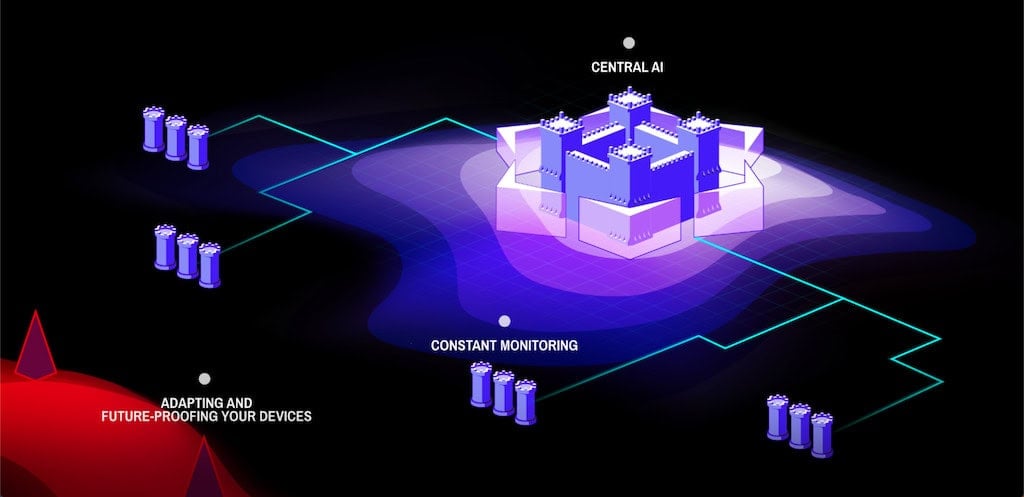
The military’s unique position enables it to develop and enforce cyber defense doctrines, leveraging decades of expertise in securing communications. These doctrines aim to prevent attacks, minimize damage when attacks occur, and identify adversaries responsible for breaches. By embedding cyber defense into the design of digitized systems, militaries can ensure their resilience against both conventional and emerging cyber threats.
The Role of the Internet of Military Things (IOMT)
IOMT represents the next frontier in military digitization, mirroring the Internet of Things (IoT) in the civilian world. This interconnected ecosystem links military personnel, systems, and platforms to combat clouds, ensuring that information flows seamlessly between users. The combat cloud serves as a repository of data, enabling faster decision-making and enhanced operational efficiency. However, this interconnectedness also introduces vulnerabilities, requiring robust cyber defense technologies to safeguard against exploitation.
As the IOMT and combat cloud evolve, adversaries may attempt to disrupt their functionality, steal sensitive data, or manipulate information to undermine operations. Cyber defense technologies must address these risks, ensuring the security and integrity of critical military systems.
Advancements in Military Cyber Defense
Cyber defense is as vital to modern militaries as ballistic protection is for personnel. The arrival of the microchip in the early 1960s initiated a steady trend of defense digitization, culminating in today’s near-total reliance on computer systems.
Bases, personnel, platforms, sensors, and weapons now depend on computerization to function effectively. This reliance is particularly evident in command and control systems like Battle Management Systems (BMSs), which move critical data such as situation reports, orders, and intelligence across the battlefield at the speed of light. Unlike in pre-digitization eras, this information no longer travels in physical form, emphasizing the military’s dependence on secure cyber domains for mission success.